Cyber Briefing: 2026.03.31
A wave of cyber incidents highlights escalating threats, from ransomware attacks and data breaches impacting major institutions to advanced phishing campaigns and exploit
👉 What's going on in the cyber world today?
Welcome to Cyber Briefing, the newsletter that informs you about the latest cybersecurity advisories, alerts, incidents and news every weekday.
First time seeing this? Please Subscribe
🚨 Cyber Alerts
1.Teampcp Pushes Malicious Telnyx On PyPI
TeamPCP has expanded its supply chain attacks by compromising the telnyx Python package with two malicious versions designed to steal sensitive data across multiple operating systems. Users are urged to downgrade to version 4.87.0 immediately as the infected versions, 4.87.1 and 4.87.2, have been quarantined on the PyPI repository.
2. TA446 Deploys DarkSword iOS Exploit
Proofpoint recently identified a Russian-aligned cyberattack using the DarkSword exploit kit to target iPhone users through deceptive emails. The operation, linked to the FSB-affiliated group TA446, used a fake invitation from the Atlantic Council to deliver GHOSTBLADE malware to high-profile figures.
3. CISA Adds CVE to KEV After F5 Exploit
CISA has added a critical remote code execution vulnerability in F5 BIG-IP Access Policy Manager to its list of known exploited flaws. Originally dismissed as a denial-of-service issue, the vulnerability is now confirmed to be under active exploitation by unknown threat actors.
For more alerts click here!
💥 Cyber Incidents
4. Dutch Police Reveal Phishing Security Breach
The Dutch National Police recently blocked a phishing attack that targeted their systems, though they maintain that no citizen or investigative data was compromised. Security experts are currently conducting a criminal investigation to determine the full scope of the breach and whether any internal employee information was accessed.
5. Stats SA Hit By Ransomware Data Leak
Statistics South Africa recently confirmed that a major ransomware attack compromised the personal information of numerous individuals seeking employment through their official channels. The breach, attributed to a group known as XP95, resulted in the theft of over 450,000 files from a database used to manage online job applications.
6. Lloyds Data Breach Hits 500K Customers
Lloyds Banking Group has issued compensation payments after a significant IT failure earlier this month compromised the private information of nearly half a million account holders. The technical error allowed customers across Lloyds, Halifax, and Bank of Scotland to view the transaction histories and personal data of other individuals.
For more incidents click here!
📢 Cyber News
7. Researcher Decompiled White House New App
The White House has launched a new mobile application on major platforms designed to provide direct access to administration updates and media. Technical analysis reveals the software is a React Native framework built using Expo and WordPress, featuring a specialized script that automatically bypasses paywalls and privacy consent banners on external websites.
8. US Charges Hacker In $53M Uranium Exploit
A crypto hacker who mocked digital assets as fake internet money is now in US custody for a fifty-three million dollar exploit that caused a decentralized exchange to collapse. Legal experts suggest this case signals a shift in how courts view smart contract exploits, moving away from the idea that technical loopholes justify theft.
9. Genesis Market: Check If You Were Targeted
In a major international crackdown known as Operation Cookie Monster, the FBI and Dutch National Police successfully dismantled Genesis Market, a massive criminal platform used to sell stolen digital identities. The National Crime Agency supported the effort by executing dozens of warrants across the UK to target users of the site and help victims secure their compromised accounts.
For more news click here!
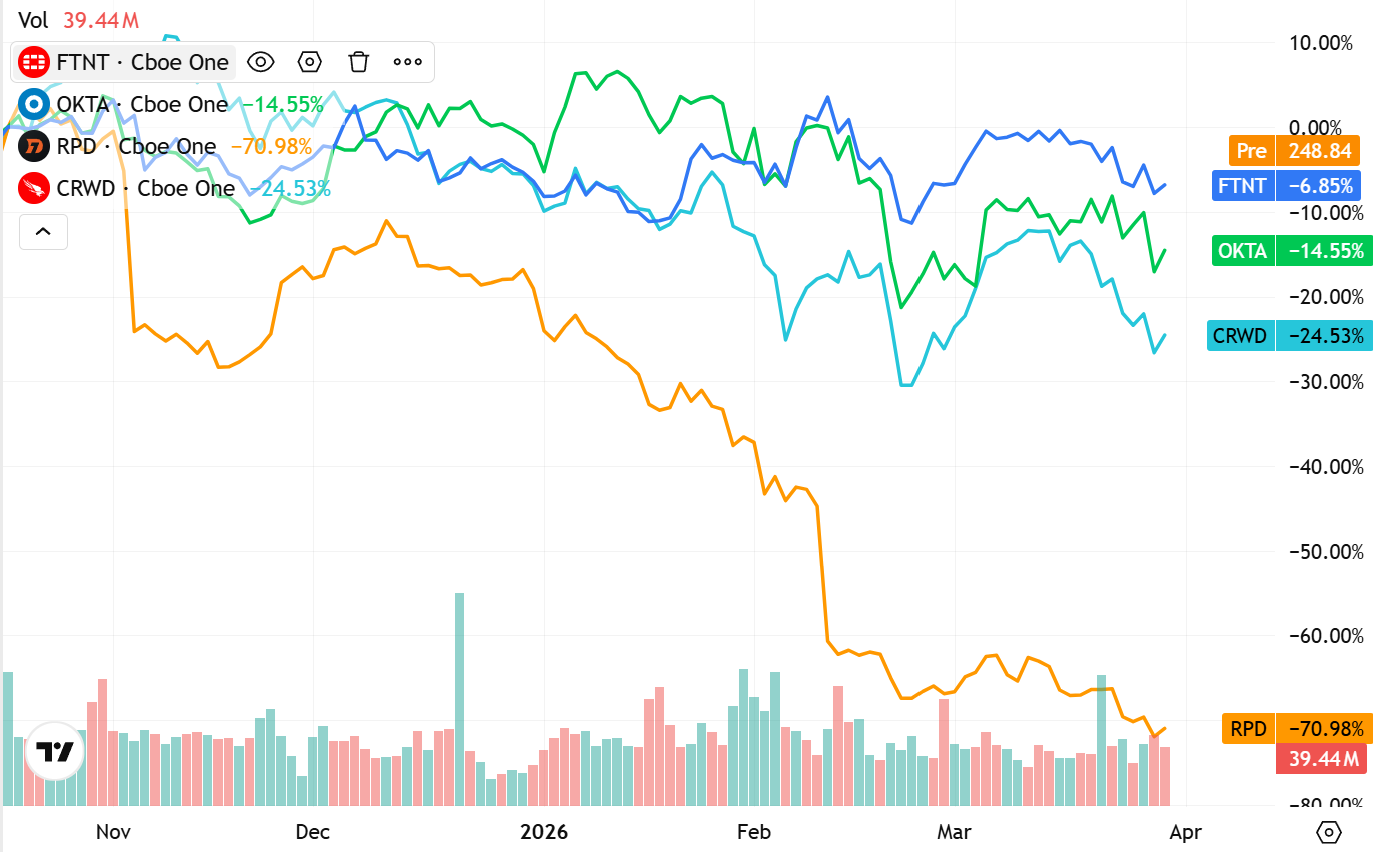
📈Cyber Stocks
Cybersecurity stocks were mixed to slightly higher on Tuesday, March 31, 2026, as the sector continued to act as a defensive hedge amid broader market volatility. Despite persistent headwinds from a partial DHS/CISA funding lapse and ongoing geopolitical uncertainty in the Middle East, high-quality security platforms saw a modest relief rally to close out the quarter.
The “flight to quality“ remains the dominant theme, with investors favoring consolidated platforms over standalone tools as enterprise “skills shortages” and AI-driven threats increase the demand for automated, integrated security.
Platform Leadership: Fortinet (FTNT) showed relative strength, finishing the period down only -6.85%, as it continues to benefit from the convergence of networking and security.
Identity Resilience: Okta (OKTA) showed signs of stabilization at -14.55%, despite a broader rotation out of high-multiple software earlier in the month, as identity remains a critical pillar of Zero Trust mandates.
Endpoint Volatility: CrowdStrike (CRWD) ended the session down -24.53% for the period. While long-term fundamentals remain robust, the stock has faced short-term pressure following a rapid valuation reset across the high-growth SaaS landscape.
Ongoing Disruption: Rapid7 (RPD) remained the primary laggard, down -70.98%, reflecting intense market skepticism toward legacy vulnerability management players in an era dominated by cloud-native security operations.
Key Insight: The “SecOps Consolidation” trend is accelerating. As seen in the recent Axios supply chain attack and the surge in Iranian-linked ransomware, organizations are prioritizing vendors that offer broad visibility across the entire attack surface rather than managing a fragmented “best-of-breed” stack.
💡 Cyber Tip
🤖 Urgent Action Required: F5 BIG-IP Remote Code Execution Vulnerability
CISA has upgraded CVE-2025-53521 to its Known Exploited Vulnerabilities (KEV) catalog following reports of active, sophisticated attacks. While initially thought to be a minor service disruption issue, this flaw is now confirmed to allow attackers full remote control over F5 BIG-IP Access Policy Manager (APM) servers.
🛠️ What You Should Do
Update Immediately: Apply the latest security patches provided by F5 to all BIG-IP APM instances to close the RCE loophole.
Audit System Integrity: Check for “fileless” webshells in system memory and inspect core utilities for unexpected file hash discrepancies or altered timestamps.
Monitor APIs and Logs: Look for unusual local user activity targeting internal management APIs or attempts to disable security features like SELinux.
Scan for Forensic Markers: Search for the presence of unexpected pipe files or suspicious HTTP traffic patterns that mimic legitimate response codes.
⚠️ Why This Matters
This vulnerability is particularly dangerous because it has evolved from a simple denial-of-service risk into a critical gateway for full network compromise. Because attackers are using sophisticated, memory-resident techniques to avoid detection, standard disk-based antivirus scans may not be enough to identify a breach.
📚 Cyber Book
Wired for Risk: The Rise of Online Gambling Addiction by Adam LeMoine
Copyright © 2026 CyberMaterial. All Rights Reserved.
Follow CyberMaterial on:
Substack, LinkedIn, Twitter, Reddit, Instagram, Facebook, YouTube, and Medium