Cyber Briefing: 2026.04.01
A series of cybersecurity incidents and developments highlight ongoing threats including supply chain attacks, malware using new persistence and delivery methods
👉 What’s trending in cybersecurity today?
Welcome to Cyber Briefing, the newsletter that informs you about the latest cybersecurity advisories, alerts, incidents and news every weekday.
First time seeing this? Please Subscribe
Listen to our podcast here ⏬
🚨 Cyber Alerts
1. Axios Attack Spreads RAT via npm Hack
The popular HTTP client Axios recently fell victim to a sophisticated supply chain attack after compromised maintainer credentials were used to publish malicious versions 1.14.1 and 0.30.4. These versions injected a trojanized dependency that targets Windows, macOS, and Linux systems, necessitating an immediate downgrade to safe versions and a rotation of all sensitive credentials.
2. DeepLoad Malware Steals Browser Data
A new campaign uses the ClickFix tactic to spread DeepLoad, a sophisticated malware loader that employs AI-generated obfuscation to bypass security scanners. Once active, the malware immediately targets browser credentials and uses advanced techniques like process injection and USB propagation to maintain a persistent, stealthy presence on infected systems.
3. Microsoft Warns Of WhatsApp VBS Malware
Microsoft has issued a warning regarding a recent cyberattack campaign that uses WhatsApp messages to spread harmful Visual Basic Script files. Starting in February 2026, this multi-stage attack establishes a permanent presence on infected devices to grant hackers remote access.
For more alerts click here!
💥 Cyber Incidents
4.Claude Code Source Leaked Via npm
Anthropic recently confirmed that a human error led to the accidental release of internal source code for its AI assistant, Claude Code, through a public package update. While no customer data was compromised, the leak exposed nearly 2,000 internal files and half a million lines of code, providing a detailed blueprint of the tool’s underlying architecture to the public.
5. Ransomware Crashes Jackson County Systems
The Jackson County Sheriff’s Office is currently rebuilding its entire computer network following a devastating ransomware attack that occurred last week. The breach has forced deputies to use paper-alternative methods for reporting and has potentially compromised critical files, including the local sex offender registry.
6. Hacker Takes Over School Facebook Page
A public school district near Schenectady is advising the community to avoid its Facebook page after a hacker took control and began sharing inappropriate videos. While local authorities and the FBI are investigating the breach, the district has confirmed that its internal servers and student data remain secure.
For more incidents click here!
📢 Cyber News
7. Android Dev Verification Rollout Begins
Google is implementing mandatory identity verification for all Android developers to prevent malicious actors from using anonymity to distribute harmful applications. This security initiative will launch in specific regions including Brazil and Southeast Asia this September before a worldwide rollout in 2026.
8. OpenAI Ends Sora App Over Deepfake Fears
OpenAI is shuttering Sora, its viral short-form video application, just months after its high-profile launch. The decision follows intense public scrutiny over deepfakes and the abrupt cancellation of a massive partnership with Disney.
9. Criminal Service Monetizes Ransomware Data
A new cybercrime platform called Leak Bazaar aims to transform raw stolen data into structured, profitable intelligence, escalating the threat of large-scale exploitation. By processing unorganized information into searchable formats, the service enables hackers to more effectively target individuals and businesses for extortion and fraud.
For more news click here!
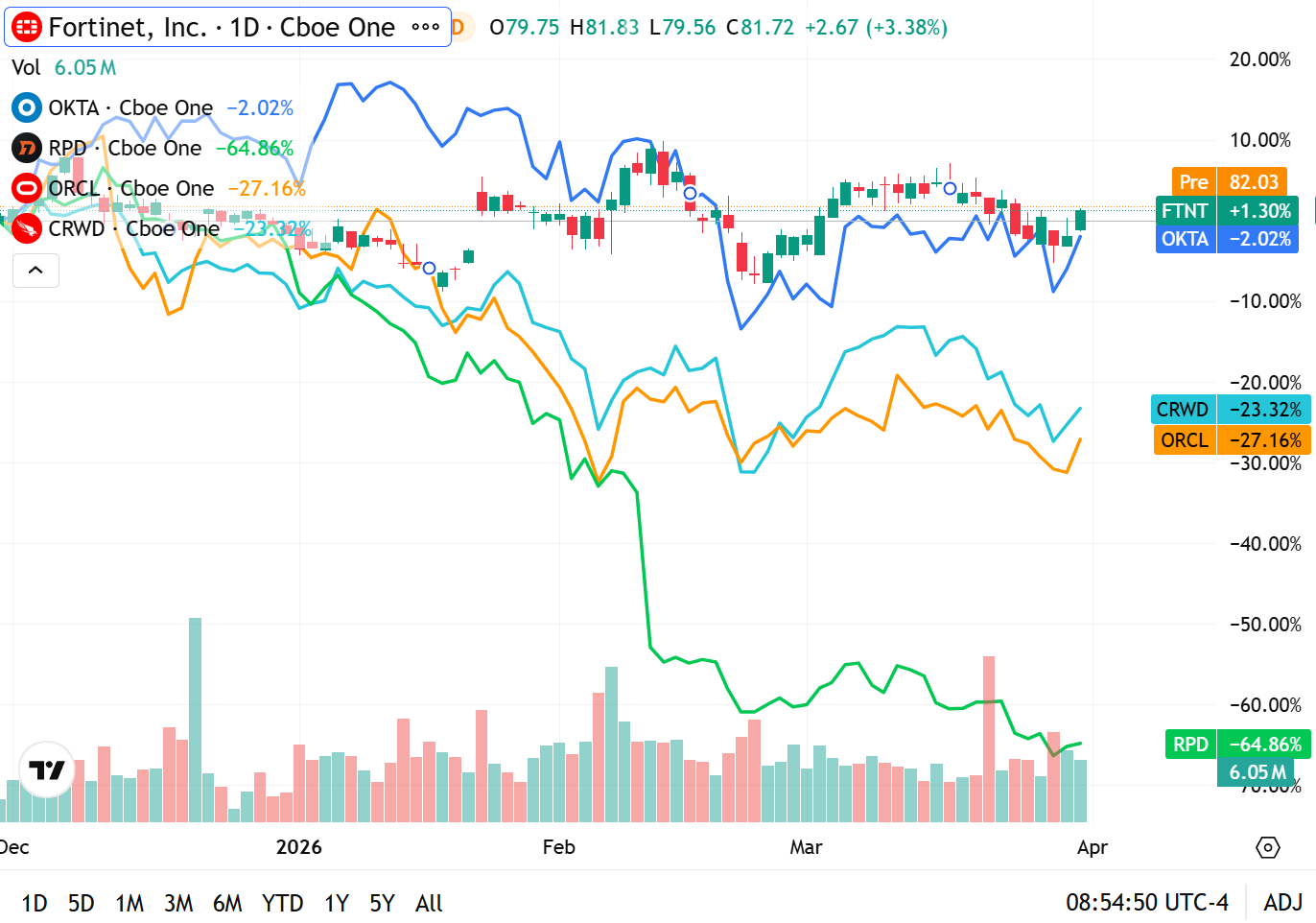
📈Cyber Stocks
Cybersecurity stocks were mixed to slightly higher on Wednesday, April 1, 2026, as the sector kicked off the second quarter with a focus on platform consolidation and cloud infrastructure security. While broader market sentiment remained cautious due to ongoing macroeconomic shifts, security “anchors” showed renewed momentum as organizations finalized their Q2 security spend allocations.
Market Summary
The start of the quarter highlights a widening gap between diversified security platforms and specialized point solutions. Investors are increasingly prioritizing vendors with integrated AI capabilities and “all-in-one” SecOps offerings.
Outperformance in Infrastructure: Fortinet (FTNT) led the pack with a solid gain, trading up +1.30% (+3.38% on the day). The stock continues to act as a sector bellwether, buoyed by the convergence of secure networking and hybrid cloud demand.
Identity Stabilization: Okta (OKTA) showed high resilience, ending the period nearly flat at -2.02%, indicating that identity access management remains a top-tier priority for enterprise risk officers.
Endpoint & Growth Pressure: CrowdStrike (CRWD) and Oracle (ORCL) saw continued volatility, trading down -23.32% and -27.16% respectively for the period. Despite the price action, CrowdStrike remains the dominant player in the AI-native XDR space, while Oracle’s security-linked cloud revenue remains a key metric for analysts.
Legacy Headwinds: Rapid7 (RPD) remained under significant pressure, down -64.86%, as the market continues to rotate away from traditional vulnerability management tools in favor of proactive exposure management platforms.
Key Insight: As we enter Q2, the narrative has shifted from “security at any cost” to “operational efficiency through security.” Large-cap winners are those successfully reducing “tool sprawl” for CISOs, a trend underscored by the relative strength of platform plays like FTNT in today’s session.
💡 Cyber Tip
Microsoft has identified a sophisticated campaign using WhatsApp to deliver malicious Visual Basic Script (VBS) files that bypass Windows security prompts. This multi-stage attack disguises itself as legitimate system tools and uses trusted cloud services to gain permanent remote access to your PC.
🛠️ What You Should Do
Verify the Sender: Never open attachments or click links in WhatsApp messages from unknown numbers, even if they look like official documents.
Check File Extensions: Be extremely wary of files ending in .vbs, .js, or .msi sent through chat apps; legitimate documents are rarely sent in these formats.
Keep Software Updated: Regularly install Windows Updates, as these often include patches for the “UAC Bypass” vulnerabilities that this malware exploits.
Use Robust Antivirus: Ensure Microsoft Defender or your preferred security suite is active, as they are being updated to flag the specific renamed tools (like “netapi.dll”) used in this attack.
⚠️ Why This Matters
This malware is particularly dangerous because it mimics standard Windows operations, making it nearly invisible to many traditional security scanners. By bypassing User Account Control (UAC), it can silently grant hackers administrative power over your computer, allowing them to steal data or monitor your activity indefinitely.
📚 Cyber Book
Gambling on AI by James Whittaker Screech
Copyright © 2026 CyberMaterial. All Rights Reserved.
Follow CyberMaterial on:
Substack, LinkedIn, Twitter, Reddit, Instagram, Facebook, YouTube, and Medium